View our Privacy Policy Here
Cracking Compliance, Empowering Data
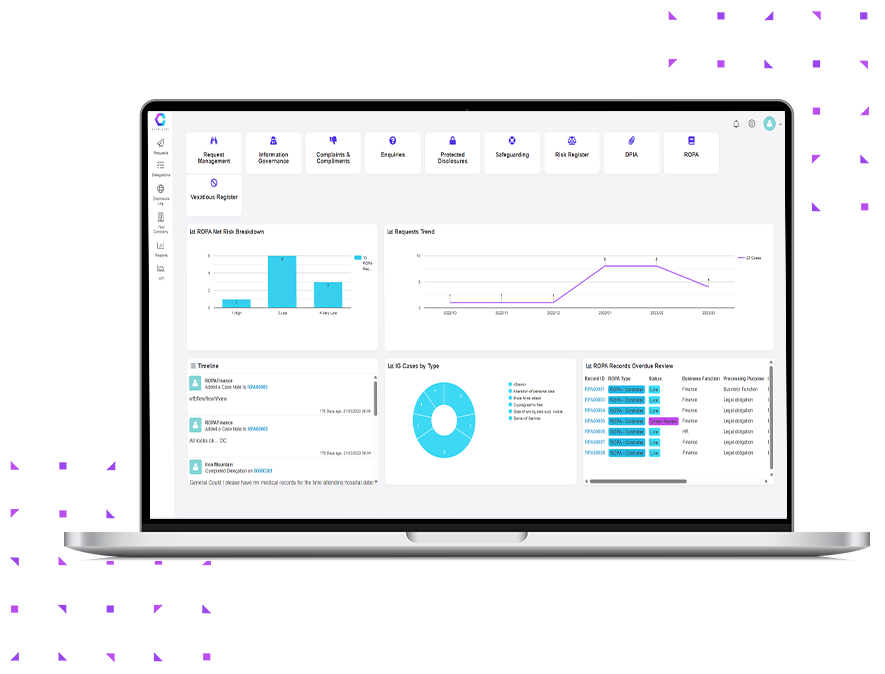
Digitalize compliance and data management with ComplyKEY! Give your organization seamless eDiscovery, efficient Data Retention, Redaction, and a range of comprehensive Data Compliance Modules, Consultancy, and Training.















ComplyKEY
Control
Navigate compliance effortlessly with modules including Data Breach, ROPA, DPIA, and Data Request Management. Includes reporting, scheduling, and E-mail integration, plus login and access management for all integrated products.
Data Request Management
Simplify and streamline the handling of AIE, EIR DSAR,FOI, FOIA, HIPPA & more

Persistent Complainants Register
A powerful tool designed to help highlight persistent and vexatious complainants

Safeguarding Management Module
Efficiently Manage Safeguarding Efforts for Enhanced Safety and Protection

ComplyKEY
Content
Seamless data retention and compliance. Confidently search, manage, and redact, data. Meet compliance obligations and industry regulations. Simplify data management, file and email archiving. Comprehensive reporting. A frictionless eDiscovery experience.

Email Archiving and eDiscovery
Simplified data compliance, efficient email archiving, and seamless eDiscovery

Data Retention & Compliance
Confidently manage your data, ensure compliance, and meet industry requirements effortlessly

Simplified Data Management
Simplified data management reporting, efficient file archiving, and seamless eDiscovery

Regulatory Compliance
Adhere to laws and industry standards ensuring data security, privacy, and ethical data handling

Redaction
ComplyKEY Redaction Powered by Smartbox.ai revolutionizes your data protection efforts with unrivaled efficiency.

Dell EMC SourceOne Alternative
Dell EMC SourceOne End of Life options. Migrate to the cloud or stay on-premises with MailMeter

Consultancy and Training
Our team of experts helps organizations establish robust Information Security Management Systems (ISMS) and craft effective compliance policies and procedures tailored to your unique needs.

Latest News
What Our Clients Say
Before engaging with ComplyKEY (Waterford Technologies), I hadn’t seen any simple and fast products to deploy email compliance management on the market. We are now saving an extraordinary amount of time and money since the deployment of MailMeter. This tool is so powerful, its search feature can scan across 22,000 mailboxes in just a few seconds and no adept training is required which eliminates the additional cost and burden from the IT department.’
‘Before ComplyKEY [Waterford Technologies] it was an absolute nightmare to archive everything, as we were using PST files to adhere to federal retention regulations. There was no centralization of data and search was impossible, [Waterford Technologies] is a blessing in disguise for the City of Pembroke Pines’
‘As Contract Owner for the MM Contract, I just wanted to note the exceptional help provided by yesterday in assisting with the query needed to support data breach investigation. Very professional, quick response and support to deal with the query, and very much appreciated. Just wanted to note for the record – great level of performance.’
I was initially drawn to Waterford Technology as I was impressed with the MailMeter and SISCIN products. The eDiscovery functionality was especially impressive in terms of both the speed of query responses and the power of the search terms that can be used. The more I worked with Waterford the more impressed I was with their responsiveness to our questions and needs, their ability to deliver and their commitment to the success of our partnership. I am confident of a long and fruitful partnership. Alec Wagner, Director, WPDM
The ComplyKEY/Evolve North partnership is a significant step forward for both organisations, working in partnership allows both organisations to provide a broader set of skills, services and solutions that will provide our clients with additional support and more importantly assist them in reducing and managing risk to data. The alignment of ComplyKEY with Evolve Norths regulatory knowledge and skills provides clients with both technical and procedural controls that are mutually supportive. This combined approach integrates these skills, services and solutions into a highly robust overarching approach to data protection.
‘We were up and running the same day. The ComplyKEY [Waterford Technologies] team has been very professional, didn’t bombard us with things we needed to do, and made the whole process painless for us. The new user interface is extremely easy, it requires no end-user training. My users are getting set up and using it without any information other than a login.’
‘The reason we chose a tool like MailMeter is that a lot of our business is based around being able to prove the facts of a discussion or a conversation.’ ‘We’ve never lost an email – ever’ ‘From a pure IT perspective, we have a clean data environment and an environment that cannot be tampered with by individual users and it gives us great comfort knowing it is there and cannot be tampered with.’
ComplyKEY is considerably faster at searching emails as opposed to the in-built search within Outlook, and that is the most important thing when searching emails …. speed. MailMeter is very popular here. MailMeter delivers back searches in a matter of seconds, and that is the most important factor to me and MailMeter users.’ ‘SISCIN indexed all files, went into the nuts and bolts, indexed every word in every file that we had, and that is crucial when doing a subject access request which we could be asked to do at any time. We ran a test and it is very good, it is like MailMeter in terms of speed’.
‘Working with ComplyKEY [Waterford Technologies], we have achieved a better way to control email & file archiving and compliance. We have removed the day-to-day burden and risk from our end users and can now provide data compliance from a centralized platform’ ‘The ComplyKEY Suite is a really valuable solution for our teams, and it has been really fast and efficient. As soon as we began using it, we started to see the benefits.’
Contact Us
Newsletter Sign Up
Copyright 2023. All Rights Reserved. Designed and Developed by Kode88 Website Design Ireland







